Smart Devices and Privacy
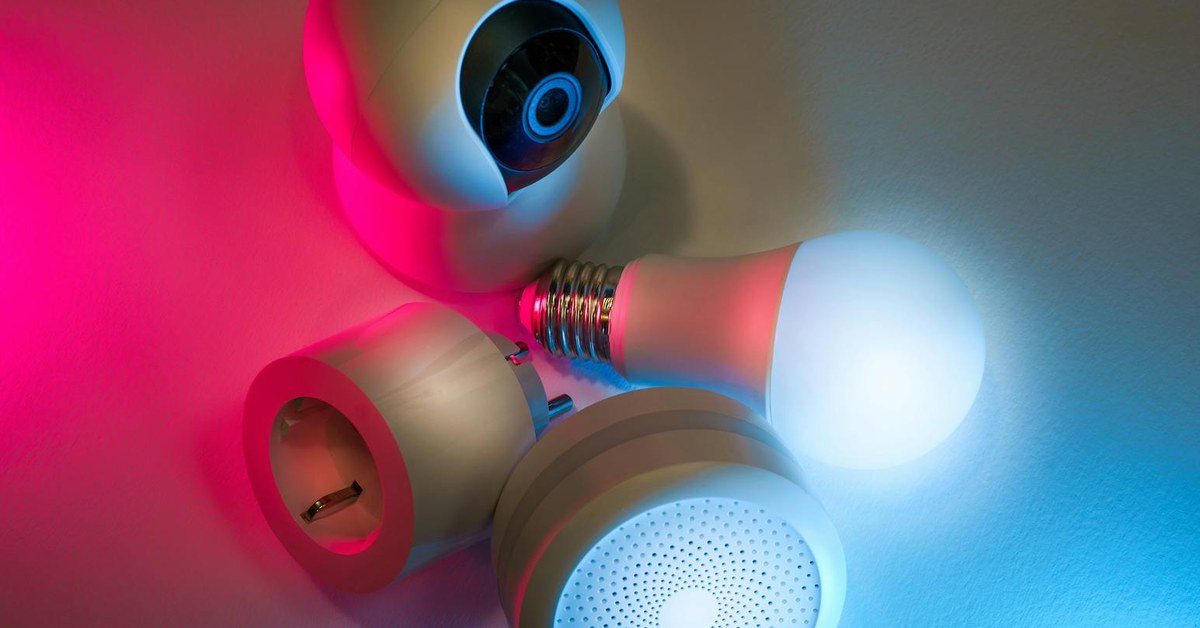
Smart speakers, connected TVs, robot vacuums and smart doorbells are everywhere. But how much data are they collecting, and what can you do to protect your privacy? A practical guide for young adults.
Smart Devices and Privacy
“Smart speakers, connected TVs, robot vacuums and smart doorbells are everywhere. But how much data are they collecting, and what can you do to protect your privacy? A practical guide for young adults.”
The Connected Home and the Privacy Bargain
Smart home technology has become a normal part of daily life for many young adults. Voice assistants answer questions and control appliances. Smart TVs stream entertainment and remember what you watch. Robot vacuums map the interior of your home. Video doorbells record who comes and goes. These devices offer genuine convenience, and their falling prices have made them accessible to people across a wide range of income levels.
But every one of these devices represents a potential privacy consideration. They collect data, some of it obviously, some of it in ways that are not immediately apparent. They connect to the internet, which means they can be accessed remotely, both by the companies that make them and, if not properly secured, by third parties. And many young adults, who may be setting up their first independent living space, have never had reason to think carefully about these issues before.
This guide is not intended to make you paranoid about technology. Smart devices can be used responsibly, and most of the time, most devices behave exactly as their manufacturers claim. What this guide does is help you understand the landscape clearly so that you can make informed decisions about what you bring into your home, how you configure it, and what trade-offs you are making.
What Data Do Smart Devices Actually Collect?
The answer varies significantly by device type and manufacturer, but some general patterns are worth understanding.
Smart speakers such as the Amazon Echo, Google Nest, and Apple HomePod are designed to listen for a wake word, at which point they begin recording and send audio to cloud servers for processing. Most do not record continuously, though there have been documented cases of devices activating in response to sounds that resemble their wake words. The audio clips that are processed are often stored on company servers and, in some cases, reviewed by human moderators for quality assurance purposes. Most major manufacturers allow users to delete this stored audio and to opt out of human review.
Smart TVs collect viewing data, including what you watch, for how long, and sometimes the apps you use. This data is typically used for targeted advertising. Many smart TV manufacturers also collect data through a technology called Automatic Content Recognition (ACR), which can identify content even when watched via an external device connected to the TV's HDMI port. This feature can usually be disabled in the TV's settings, though the option is sometimes buried.
Smart doorbells and security cameras capture video and audio of activity around your home. This footage may be stored locally or in the cloud. Some manufacturers, notably Ring (owned by Amazon), have had significant controversy around sharing footage with law enforcement agencies without explicit consent from the device owner, though policies have evolved in response to public pressure. Understanding your manufacturer's data-sharing policies is important before installing any camera device.
Robot vacuums with mapping features create detailed floor plans of your home, which are stored and in some cases shared with the manufacturer. In 2022, reports emerged of internal images from iRobot's development devices appearing online, prompting significant debate about the data practices of household robotics companies. This is a relatively new area of concern but one worth being aware of.
Securing Your Home Wi-Fi Network
Your home router is the gateway through which all your smart devices access the internet. A poorly secured router is one of the most significant vulnerabilities in any smart home setup, and improving router security is one of the highest-value actions you can take.
The first step is changing your router's default administrator password. Many routers come with a default password printed on the device, and these default passwords are publicly known. If an attacker gains access to your router's admin interface, they can potentially monitor all traffic on your network and manipulate your connected devices. Change the admin password to something long, unique, and not easily guessable.
Use a strong Wi-Fi password. WPA3 encryption is the current standard, and WPA2 is widely considered acceptable. Avoid WEP encryption, which is outdated and easily compromised. Your Wi-Fi password should be at least twelve characters long and include a mixture of letters, numbers and symbols.
Consider setting up a separate guest network for your smart devices. Many modern routers allow you to create a second network that is isolated from your main network. Placing smart devices on a separate network means that if one device is compromised, the attacker cannot easily use it to access your laptop, phone, or other devices containing sensitive personal information. This is a relatively simple configuration change available on most modern routers and provides meaningful additional security.
Keep your router's firmware updated. Manufacturers release firmware updates that patch security vulnerabilities, but many routers do not update automatically. Log into your router's admin interface periodically to check for updates, or enable automatic updates if your router supports them.
Voice Assistants: Practical Privacy Steps
If you use a voice assistant, there are several straightforward steps you can take to reduce your data exposure without significantly limiting the device's usefulness.
Review and delete stored audio recordings regularly. Amazon, Google, and Apple all provide tools in their respective apps or web interfaces that allow you to view, listen to, and delete audio recordings associated with your account. Set a reminder to do this periodically, or configure the device to delete recordings automatically after a set period.
Opt out of human review of your voice recordings if this option is available in your device settings. Most major manufacturers offer this option following public pressure and regulatory scrutiny.
Use the physical mute button when you do not want the device to be listening. Smart speakers have hardware mute buttons that physically disconnect the microphone, providing a higher level of assurance than a software-based mute, which could in theory be overridden by a software vulnerability.
Consider where you place voice-activated devices. Positioning them away from areas where you have private conversations, such as your bedroom or a home office, reduces the risk of sensitive conversations being captured, whether accidentally or otherwise.
Smart TVs: Disabling Data Collection
Smart TV privacy settings vary by manufacturer and model, but the following steps apply broadly across most devices.
Disable Automatic Content Recognition (ACR) in your TV's settings. This feature may be labelled differently depending on the manufacturer; Samsung calls it "Viewing Information Services," LG calls it "LivePlus," and Vizio calls it "Smart Interactivity." Look for these options in the privacy or settings menu and disable them.
Opt out of targeted advertising through your TV's settings. Most smart TVs offer the ability to limit ad tracking, similar to the equivalent option on smartphones. This does not eliminate advertising but reduces the amount of data used to target it.
Review the privacy policy for your TV's operating system. Whilst reading an entire privacy policy is rarely practical, looking for sections related to data sharing with third parties and data retention policies is worth doing for a device that sits in your living room and monitors your viewing habits.
If you are privacy-conscious and primarily use streaming services accessed via a separate device such as an Apple TV, Chromecast, or games console, you may choose to disable or avoid using the smart TV's built-in functionality altogether, using it only as a display.
Smart Doorbells and Cameras
Video surveillance devices around your home raise both personal privacy concerns and potential legal considerations. In many countries, recording audio or video of people in public spaces or shared areas of buildings is subject to specific rules, and it is worth understanding the relevant regulations in your jurisdiction before installing cameras.
Enable two-factor authentication on any app-based security camera or doorbell system. This means that even if someone obtains your password, they cannot access your camera feeds without also having access to your phone or email. Most camera manufacturers support two-factor authentication; enable it.
Use strong, unique passwords for your camera system account. Reusing passwords across multiple accounts is one of the most common causes of account compromise. If you use the same password for your camera system and another service that suffers a data breach, your cameras could be accessed remotely by a third party.
Review your camera's cloud storage settings and understand who can access stored footage. Some manufacturers have had partnerships with law enforcement that allowed access to footage without the explicit consent of the device owner. If this concerns you, look for devices that offer local storage options and review the manufacturer's law enforcement data request policy.
Regularly check whether your camera system's firmware is up to date. Security vulnerabilities in camera firmware have been discovered and exploited in a number of high-profile cases. Keeping firmware updated reduces this risk.
Passwords and Account Security Across All Devices
Most smart devices are linked to manufacturer accounts, which means the security of those accounts directly affects the security of the devices. The following practices apply across all connected device accounts.
Use a different password for every account. This is the single most impactful thing you can do for your overall online security. If one service you use suffers a data breach and your password is exposed, unique passwords mean that only one account is compromised rather than all of them.
Use a password manager to generate and store strong, unique passwords. Password managers such as Bitwarden, 1Password, and others make it practical to have unique complex passwords for every account without needing to remember them all. Many are free or low-cost, and they are available across all major platforms.
Enable two-factor authentication on all accounts where it is available, not just camera systems. Your smart home app accounts, email, and any other account associated with home devices should all use two-factor authentication where possible.
Data Brokers and Smart Device Data
An aspect of smart device privacy that receives less attention than it deserves is the relationship between device manufacturers and data brokers. Data brokers are companies that collect personal data from a wide range of sources, combine it, and sell it to third parties including advertisers, insurers, and other organisations.
Some smart device manufacturers sell or share data with data brokers, adding smart home usage patterns to profiles that already include location data, browsing history, and purchase history. This aggregated data can create remarkably detailed pictures of people's daily lives, habits, and preferences.
Whilst it is difficult to fully remove your information from data broker databases, there are services that assist with this process. In many countries, data protection regulations give individuals the right to request that organisations delete their personal data. In the UK, the Information Commissioner's Office provides guidance on these rights. In the European Union, the General Data Protection Regulation (GDPR) provides robust rights in this area. In the United States, the legal framework varies by state, with California's Consumer Privacy Act (CCPA) being among the strongest protections available.
Updates and Long-Term Device Security
One of the less glamorous aspects of smart device security is maintenance. Devices that are not updated become progressively more vulnerable as new security research reveals weaknesses that were not known when the device was manufactured.
Enable automatic updates where available. Many smart devices and their associated apps offer automatic update settings that ensure security patches are applied promptly. This is the single easiest way to maintain security over time.
Be aware of end-of-life timelines for smart devices. Manufacturers typically support devices with security updates for a defined period, after which they are no longer patched. A smart device that is no longer receiving security updates is a device with known, unpatched vulnerabilities. Research the support lifecycle of devices before purchasing, and consider replacing devices that have reached end-of-life status, particularly those with direct access to your home network or the ability to capture audio and video.
When disposing of old smart devices, perform a factory reset to remove your personal data and account credentials before passing them on or recycling them. Devices sold or given away without being reset may retain data that the next owner could access.
Making Informed Choices
None of this should put you off using smart home technology altogether. The convenience these devices offer is real, and for many people the trade-offs are acceptable. What matters is that you are making those trade-offs knowingly rather than by default.
Before buying a new smart device, spend five minutes researching its data practices. Look for clear privacy policies, a track record of releasing security updates, and the availability of local storage options for devices that capture audio or video. User reviews and technology journalism often surface privacy concerns that are worth knowing about before purchase.
Review the permissions granted to smart device apps on your phone. Many apps request access to location, microphone, camera, and contacts that may not be necessary for their core function. Reviewing and restricting these permissions is a quick way to reduce your data exposure.
Stay informed. The smart home technology landscape changes rapidly, and privacy practices that are acceptable today may change as companies update their policies or are acquired by larger organisations. Following technology privacy reporting from outlets such as the Electronic Frontier Foundation, Privacy International, or equivalent national organisations keeps you informed without requiring deep technical expertise.
Your home should be a place of genuine privacy and safety. Taking the time to secure your smart devices is not paranoia; it is a reasonable and proportionate response to the real data practices of the technology industry.